What is identity verification? A comprehensive overview
Identity verification is the process that confirms you are who you claim to be before you’re granted access to services, accounts, or restricted areas.
Outside of physical paper-based documentation and manual checks, organizations use methods like document scanning, facial recognition, and database checks to confirm identities.
In this guide, we explain what identity verification is, how it works, and why it matters. We'll cover the most common verification methods, compare their strengths and limitations, explore the regulations that govern identity checks, and discuss the privacy implications of collecting and processing personal data.
What is identity verification?
Identity verification involves comparing information provided by a user against trusted sources. This might include checking a government-issued ID, validating personal details against official databases, or confirming control over an email address or phone number.
There are two main types of identity verification: traditional (physical) and digital.
Traditional identity verification happens in person. You’re required to present your documents physically, and then someone manually inspects them or validates them against official records.
Digital identity verification uses technology to confirm identities remotely. Instead of presenting documents in person, users submit information through websites, mobile apps, or online platforms, including uploading photos of identity documents, selfies for facial recognition, answering knowledge-based questions, or verifying control over an email address or phone number.
Confirming your identity digitally makes it possible to open accounts, verify transactions, or complete compliance checks from anywhere.
In many cases, organizations rely on third-party identity verification providers to handle these checks securely and at scale. These providers have advanced systems that can analyze document security features like holograms and microprinting, compare facial features against photo IDs, and cross-reference information with government or trusted databases.
Identity verification vs. identity authentication vs. identity validation
While these three terms are related, they describe different steps in managing digital identity:
- Identity verification: The initial process of confirming that a person’s claimed identity is legitimate. This usually happens once, at the beginning of a relationship, like when registering for an online account.
- Identity validation: Checks whether the identity information provided is real and accurate. An example is confirming that a Social Security number exists in government records or that an address is a real location. Validation happens during verification to ensure the claimed identity corresponds to a real person.
- Identity authentication: Happens after verification and validation. It confirms that a returning user is the same person who previously verified their identity. This happens repeatedly, like each time you log into your email using a password or fingerprint. Identity authentication assumes the identity has already been verified and focuses on proving the returning user is still the legitimate account holder.
| Identity verification | Identity authentication | Identity validation | |
| Purpose | Confirms a person’s claimed identity is legitimate | Confirms a returning user is the same verified person | Confirms identity data is real and accurate |
| When it happens | At the start of a relationship (account creation, onboarding) | Every time access is requested | During verification or when identity data is updated |
| What it checks | Whether the person is who they claim to be | Whether the user can prove ownership of the account | Whether provided details exist and match official records |
| Example | Uploading a government ID during account registration | Logging in with a password, OTP, or fingerprint | Checking if a Social Security number exists in a government database |
The importance of identity verification
Identity verification supports trust in digital services for both users and organizations. It allows organizations to accurately confirm who is accessing an account or requesting a transaction while making online accounts and transactions more secure for users.
How does identity verification protect users?
Identity verification benefits users by strengthening account protection and reducing identity-related fraud. When platforms verify identities during registration or high-risk actions, they limit opportunities for impersonation. This reduces the likelihood of someone creating an account in another person’s name or gaining access through false information.
In addition, identity verification supports more reliable digital interactions, as verified user profiles can increase trust in peer-to-peer marketplaces and online communities.
Why is identity verification critical for businesses?
For businesses, identity verification plays a key role in risk management, compliance, and operational security.
First, regulatory compliance requires many industries to verify customer identities. For instance, financial institutions must follow Know Your Customer (KYC) regulations that require them to confirm the identity of clients before opening accounts.
Beyond compliance, identity verification helps businesses:
- Reduce identity fraud: Confirming identity at onboarding lowers the risk of fake accounts and synthetic identities.
- Protect account integrity: Strong verification reduces unauthorized access and account takeovers.
- Build customer trust: Verification processes signal that an organization protects its platform from bad actors. This is especially important for platforms where users interact with each other, like marketplaces or social networks.
In regulated industries, non-compliance with identity verification requirements can result in substantial fines, regulatory sanctions, legal action, or even the loss of operating licenses. Over time, repeated security incidents and fraud resulting from a lack of identity verification can erode customer trust, damage brand reputation, and drive users toward competitors.
How identity verification works
While specific steps vary depending on the verification method, service requirements, and risk level, most systems follow a similar framework.
At a high level, the process involves collecting identity information, checking it against trusted sources, and determining whether the identity is valid and belongs to a real person.
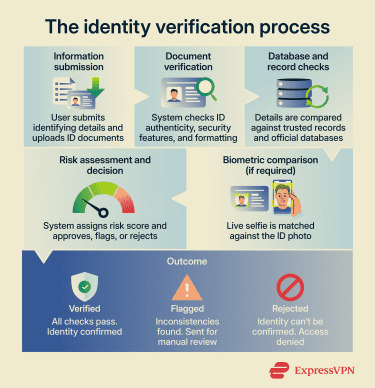
Key steps in an identity verification process
Many identity verification processes follow these core steps:
- Information submission: The user submits identifying information. This may include their full name, date of birth, address, government-issued ID number, or a photo of an identity document.
- Document verification: The system checks whether the uploaded ID appears authentic. This might include analyzing security features, such as machine-readable zones (the coded lines of text typically found at the bottom of passports and some national IDs) and holograms that are embedded in many government-issued documents to prevent tampering. It might also involve verifying that the document’s layout and formatting match official standards.
- Database and record checks: Submitted details are compared against trusted data sources, such as credit bureaus, government records, or other verified databases. This can help detect fabricated identities even when someone presents convincing fake documents.
- Biometric comparison: The user may be asked to take a selfie. The system’s facial recognition software compares the live image to the photo on the ID to confirm they match.
- Risk assessment and decision: The system evaluates results and assigns a risk score. If all checks pass, the identity is verified. If inconsistencies appear, the case may be flagged for manual review or rejected.
What information is typically checked during verification?
The specific data checked depends on the service and regulatory requirements. However, most identity verification systems review a combination of the following:
- Personally identifiable information (PII): This includes full legal name, date of birth, residential address, and government-issued identification numbers like Social Security numbers or passport numbers.
- Identity documents: Driver's licenses, passports, national ID cards, and birth certificates are commonly checked document types.
- Biometric data: This includes photos, fingerprints, voice samples, etc.
- Contact information: Email addresses, phone numbers, and even social media accounts help confirm that users are reachable and control the accounts they claim.
- Device and network data: Systems may check the device being used, IP address location, browser fingerprint, and connection patterns. Unusual patterns, like accessing an account from a different country, trigger additional verification steps.
Methods of identity verification
Different organizations use different user verification methods depending on their security requirements, user convenience needs, and regulatory obligations. Each method has distinct strengths and limitations, and many services combine multiple methods to create more robust verification systems.
Below are the most common methods used in modern identity verification.
ID document verification
ID document verification involves analyzing a government-issued document, such as a passport, driver’s license, or national ID card. Users typically upload a photo or scan of their ID.
This method is widely used in KYC identity verification and anti-money laundering (AML) identity verification programs.
Document verification provides strong evidence of identity since government-issued IDs undergo formal identity checks before issuance. Plus, it works across borders, as passports and many national IDs are widely recognized internationally.
However, on its own, it may not confirm that the person presenting the ID is its rightful owner. Someone could use a stolen or borrowed ID that passes authenticity checks but doesn’t belong to them. Additionally, sophisticated counterfeit documents can sometimes pass automated checks. To make it more reliable, many systems combine document checks with biometric verification.
Biometric verification
Biometric verification uses unique physical traits to confirm identity. In digital identity verification, facial recognition is a common approach. The system compares a live selfie or short video capture to the photo on an identity document or to a previously stored template.
Modern systems usually include liveness detection, which checks that the image comes from a real person present in front of the camera rather than a static photo. The verification app may ask the user to blink, turn their head, or follow a moving prompt on the screen, or it may analyze subtle signals like depth, lighting reflections, and facial micro-movements.
One main advantage of biometric verification is that it’s harder to impersonate someone compared to passwords or documents alone. Even if someone stole a passport and found a photo of the owner online, most identity verification systems require a live camera capture, making it difficult to authenticate using a printed image or social media photo.
On the flip side, biometric data raises privacy concerns since it's permanently tied to an individual and can't be changed like a password. Therefore, organizations using this method must store and process biometric data securely.
Additionally, environmental factors like poor lighting or background noise can affect accuracy. Some users may also be unable to provide certain biometrics due to physical characteristics or disabilities.
Knowledge-based authentication
Knowledge-based authentication (KBA) verifies identity by asking security questions that the legitimate user is expected to answer correctly. These may include previous addresses, pet names, loan or credit history details, or account-related information.
KBA has been widely used in financial services and account recovery processes. However, it’s increasingly considered weaker than other methods since public data exposure and data breaches have made personal information easier to obtain. For instance, social media makes it easy to find information like a mother's maiden name, pet names, or schools attended. In addition, attackers may use social engineering tactics to trick individuals into revealing this information without realizing it.
As a result, KBA alone may not provide strong identity fraud prevention. Many organizations now use it only as a secondary measure or have entirely replaced it with stronger identity authentication methods.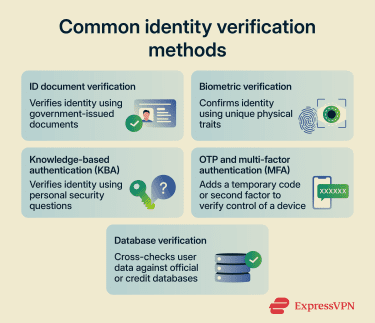
One-time passcodes and multi-factor verification
One-time passcodes (OTPs) and multi-factor authentication (MFA) add an extra verification step beyond passwords. While they’re commonly used for identity authentication, they can also support identity verification during onboarding or high-risk transactions.
For OPTs, systems generate temporary codes valid for a short time, typically 30 seconds to 2 minutes. These codes are sent via SMS, email, or generated by authenticator apps. Users enter the code along with their regular password to prove they control the registered device or email account.
Multi-factor verification requires users to provide two or more different types of credentials. Common combinations include password plus OTP, password plus fingerprint, or password plus security key.
Multi-factor verification generally increases security compared to passwords alone. Even if someone steals a password, they can't access the account without the second factor. OTPs expire quickly, limiting the window for attackers to use stolen codes.
That said, SMS-based OTPs can be intercepted through SIM swapping attacks, where criminals trick phone carriers into transferring a number to a different device. Additionally, users might lose access if they don't have their phone or can't receive messages. The additional verification step also creates a slight inconvenience, though most users accept this trade-off for better security.
Database verification
Database verification cross-references provided information against authoritative data sources like government databases, credit bureaus, or telecommunications records. This method confirms that identity information exists in official systems and matches across multiple sources. For example, it might verify a Social Security number exists, confirm an address appears in postal records, or check that a phone number is registered to the stated name.
In many implementations, database verification runs in the background without requiring additional user steps beyond providing basic information. It catches many fraud attempts since fabricated identities won't have records in multiple authoritative databases. It also scales efficiently, as it’s capable of handling large volumes of verification requests automatically.
However, database verification depends on data accuracy, and errors in databases can lead to false rejections of legitimate users. Coverage gaps exist for certain populations, such as people who recently immigrated or young adults without a credit history. Privacy concerns also arise around accessing personal information from multiple sources without explicit user consent for each lookup.
Identity verification regulations and standards
As mentioned above, in many industries, identity verification is a legal requirement. Governments and regulatory bodies set standards that define how organizations must verify identities, store personal data, and prevent financial crime.
Several major regulations shape how organizations implement identity verification systems worldwide.
- KYC requirements: These apply primarily to financial institutions. They require banks, investment firms, and cryptocurrency exchanges to verify customer identities before opening accounts or processing significant transactions. The goal is to prevent money laundering, terrorist financing, and other financial crimes.
- AML regulations: These extend beyond basic identity verification to include ongoing monitoring of customer activities. Organizations must verify identities at onboarding and continue watching for suspicious patterns that might indicate money laundering.
- Children's Online Privacy Protection Act (COPPA): This law requires websites and online services to verify users' ages and obtain parental consent before collecting personal information from children under 13. Age verification has become a growing focus as more jurisdictions implement similar requirements to protect minors online.
- Electronic Identification, Authentication and Trust Services (eIDAS): It establishes standards for electronic identification and trust services across the EU. eIDAS creates a framework for mutual recognition of electronic identities across EU member states, making it easier for organizations to verify identities across borders within Europe.
Privacy considerations
While identity verification supports fraud prevention and regulatory compliance, it also involves handling sensitive personal data. This creates important privacy considerations. Organizations must ensure that identity verification services:
- Collect only the information necessary for verification purposes.
- Use verification data only for its stated purpose.
- Use secure storage and encryption.
- Use access controls to prevent unauthorized access to user verification data.
- Comply with regional data protection laws.
Transparency is also important. Users should understand why identity verification is required, what data is being collected, and how it will be used.
Additionally, when identity verification is handled by a third-party provider, organizations must carefully vet that provider’s security practices, data handling policies, and regulatory compliance.
In practice, identity verification regulations aim to balance the need to prevent fraud with the need to protect personal data. Organizations must design their verification processes to meet both requirements without over-collecting information or introducing unnecessary risk.
Identity verification vs. age verification
Identity verification and age verification are closely related, but they serve different purposes. Identity verification aims to establish a person’s real-world identity with a high level of confidence. Age verification, in contrast, confirms whether someone meets a specific age requirement.
In some cases, age verification relies on full identity verification. For example, a platform may require users to upload a government-issued ID to confirm they are over 18. In this scenario, the system verifies both identity and age simultaneously.
However, not all age verification systems require full identity checks. Some methods, such as reusable digital credentials and zero-knowledge proofs, allow users to confirm they meet an age requirement without revealing their exact date of birth.
This distinction is becoming increasingly important as more jurisdictions introduce laws aimed at protecting minors online. Regulations such as the COPPA in the U.S. and similar frameworks in other regions require platforms to take steps to verify age or obtain parental consent in certain situations.
The future of identity verification
As digital services expand and fraud tactics grow more sophisticated, organizations are adapting their identity verification systems in response.
Industry trends suggest that identity verification is moving toward greater automation, stronger data protection, and improved interoperability between systems. New technologies are expanding the capabilities and changing the characteristics of identity verification systems. These include:
- Reusable digital credentials: Users verify their identity once with a trusted authority and receive a cryptographically signed digital credential, typically backed by public key infrastructure (PKI) or similar asymmetric cryptography frameworks. They can use this credential across multiple services without having to upload documents repeatedly. Services confirm authenticity through digital signature validation using the issuer’s public key rather than contacting the issuer each time.
- AI-driven verification: AI and machine learning improve verification accuracy and speed. They detect forged documents, identify subtle fraud patterns, and adapt to new attack methods. However, AI-driven verification requires careful implementation to reduce bias and ensure fairness across demographic groups.
- Behavioral biometrics: These systems analyze how users interact with devices, such as typing patterns, swipe gestures, and mouse movements. The behaviors are difficult to replicate and allow continuous, passive verification. Unusual activity is flagged because it may indicate someone else is using the account. This approach adds security without creating friction since users don't need to stop and complete verification steps.
- Passwordless authentication: This approach replaces traditional passwords with passkeys or device-based credentials stored on user devices. It is more secure and convenient since users don’t need to remember complex passwords, and the risk of phishing is minimal.
- Zero-knowledge proofs: This technology allows users to prove specific facts without revealing underlying personal data. For example, someone can confirm they’re 18 or older without sharing their exact age. It’s designed to support privacy-focused verification while minimizing the amount of data shared.
While many of these technologies are still developing, they reflect a broader shift toward secure and privacy-aware identity verification systems. Without liveness detection, someone could attempt to bypass biometric verification by impersonating another using a printed photo, a video replay, a mask, or even AI-generated deepfake images or videos designed to mimic someone’s facial movements. Liveness detection systems analyze subtle signals such as natural facial movement, depth perception, texture patterns, lighting changes, or prompted actions like blinking, smiling, or turning the head. These checks reduce the risk of spoofing attempts during online identity verification.
However, these privacy-preserving methods are still developing, and many current verification systems collect personal information to meet security and regulatory requirements. For instance, many regulated industries still require the collection of specific identifying information to meet Know Your Customer (KYC) or anti-money laundering (AML) identity verification obligations.
FAQ: Common questions about identity verification
What is an example of identity verification?
What is liveness detection and why does it matter?
What’s the difference between identity verification and authentication?
What is the difference between identity proofing and identity verification?
Is identity verification the same as logging in with a password?
Does identity verification mean a company permanently stores my ID or biometric data?
Can identity verification work without collecting sensitive personal data?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN